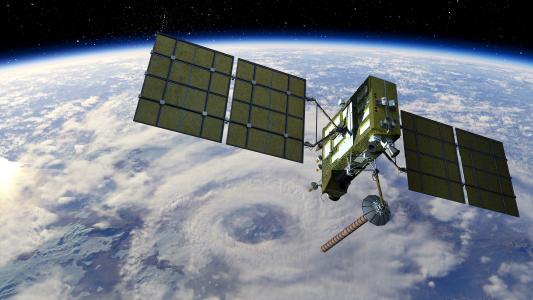
Satellites are a key component of the United States’ military operations — they play a role in navigation, communication, intelligence gathering, and more.
In an attempt to get ahead of any cyber attacks on these valuable assets, the U.S. Air Force is hosting Hack-A-Sat, an ethical hacking competition to try to find security vulnerabilities in satellite systems — and awarding hackers $250,000 in prizes if they’re successful.
Calling All White Hat Hackers
Hacking is generally associated with malicious activity — the hooded stereotype of a computer geek clacking away at a keyboard, probing for computer vulnerabilities to steal someone’s identity or install ransomware on their system.
But those aren’t the only types of hackers. Others — known as “white hat” hackers — also look for security vulnerabilities, but for the purpose of identifying them so that they can be fixed, not exploited.
It’s those ethical hackers that the Air Force is hoping to draw to Hack-A-Sat.
When the event was first announced, the plan was for Hack-A-Sat to take place at DEF CON, an annual hacking convention. Due to the coronavirus pandemic, DEF CON has cancelled all in-person activities, but the Air Force is still moving forward with Hack-A-Sat as a virtual event.
The ethical hacking competition will be divided into two rounds.
The first is a qualification round that will take place from May 22 through 24. In this round, teams of hackers will compete in a Jeopardy-style game, where they can earn points for solving satellite-related problems in six potential categories, including “Payload Modules” and “Communications Systems.”
At the end of that round, the 10 highest-ranked teams will be given three weeks to submit a technical paper detailing how they solved at least five of the challenges. In exchange, they’ll each receive $15,000.
The teams will then move on to the final round of the ethical hacking competition, which will take place August 7 through 9. Only eight of the teams will have a chance to compete, though — the two with the lowest scores in the qualifying round will serve as alternates.
Initially, teams who made it to this final round were supposed to have a chance to hack a real satellite — as in, one currently orbiting the Earth. Now that the event is fully virtual, they’ll have to settle for hacking “representative ground-based and on-orbit satellite systems,” according to a May 13 update.
Teams will earn points for completing challenges, and the winners will earn $50,000 for first place, $30,000 for second place, and $20,000 for third place — but only after they submit a technical paper, once again explaining how they beat the code.
Ethical Hacking for the Gov’t
Hack-A-Sat won’t be the military’s first collaboration with white hat hackers. In 2016, the Department of Defence launched “Hack the Pentagon,” an ethical hacking pilot program that marked a turning point in the nation’s approach to cybersecurity.
“Up until very recently, the government’s way of keeping people in the U.S. from hacking them was to basically threaten that black helicopters would show up over your house if you tried,” program participant Dan Tentler told Wired in 2017. “Then one day I’m stuck at the airport and I’m brute-forcing various Pentagon hosts with no fear of repercussions. It’s pretty cool.”
Working with ethical hackers has been, and continues to be, a win-win.
Kristopher Johnson
That pilot program evolved into the Vulnerability Disclosure Program (VDP), which has received tens of millions of dollars in funding from the DOD. The investment is paying off, too — in 2019 alone, white hat hackers submitted more than 4,000 security vulnerabilities through the VDP.
“Working with hackers to improve an organization’s cyber hygiene was considered a revolutionary idea in 2016, but it has evolved to become almost commonplace in DOD,” VDP Director Kristopher Johnson said in a blog post.
“Working with ethical hackers has been, and continues to be, a win-win,” he added.
We’d love to hear from you! If you have a comment about this article or if you have a tip for a future Freethink story, please email us at [email protected].